OUR OBJECTIVE. OUR INTEGRATED MANAGEMENT SYSTEM (TIMS).
When your objective is to achieve something together in cooperation with various brands, countries and people, this is only possible if each party shares the same values and principles.
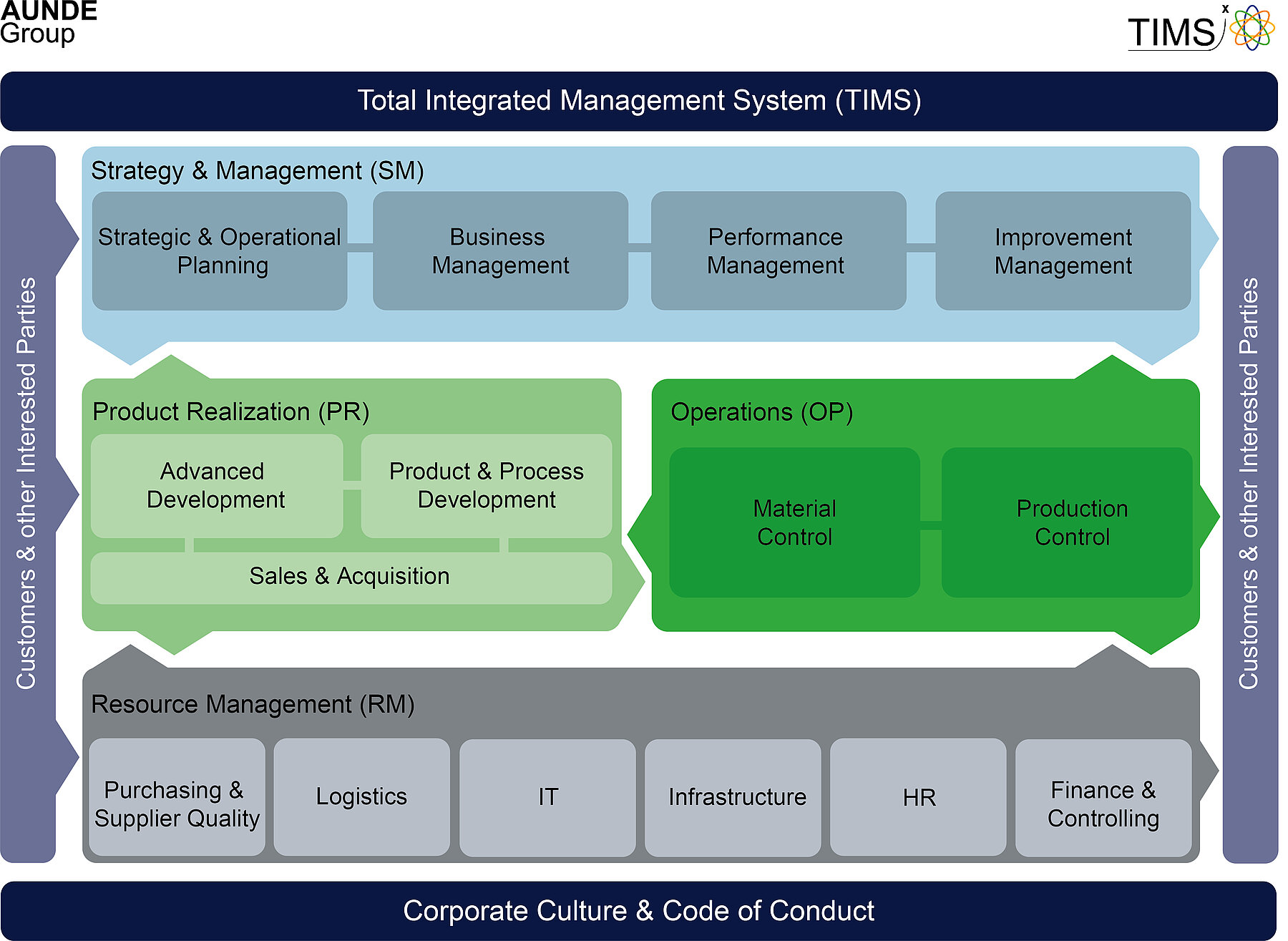
Our total integrated management system (TIMS) is used by our whole group and encompasses our strategic orientation as well the common maxim for our daily work. Our procedure architecture is based on international standards. The modular design increases transparency and the flexibility of the system enables it to adapt to future demands. Our focus is on the creation of a high value chain – this means customer focus and sustainability must go hand in hand.
THE HISTORY OF OUR INTEGRATED MANAGEMENT SYSTEM
Our TIMS is not a recent invention, but rather it is the contemporary version of what used to be known as operation regulations and corporate code of practice. In their day, these regulations served our company as a steering and control instrument. Our current TIMS Manual, in combination with the AUNDE Code of Conduct, replaces the company regulations as a Group-wide guideline.
Would you like to find out more about the evolution of our management system? In the download area on this page you will find our historical regulations, our Code of Conduct and also a description of TIMS in the Management System Essentials.
Information security
Due to increasing digitalization, securing information and systems is an essential factor in ensuring uninterrupted support for business processes. Ensuring information security is therefore an essential success factor for the AUNDE Group.
Our guiding principles
The protection of sensitive customer and company data is of paramount importance to the business success of the AUNDE Group and all its Business Units. Therefore maintaining a risk-based approach to information security is an essential and inseparable part of the business strategy of AUNDE Group with all its subdivisions. The aim of information security is to protect the data and information of the AUNDE Group adequately, effectively, and consistently against threats. Doing so, it is essential to protect them appropriately against information security breaches at all levels and in all states.
Management commits itself to
- preserving information from loss of integrity, confidentiality, and availability all times - in the interest of all parties involved
- determining the required level of information security, considering economic aspects, according to the need for protection of the information and to implement this need for protection with available, future-proof technology and the appropriate organizational measures
- requiring all employees of the company to comply with the Information Security Policy and its subordinate documents – and to comply with these themselves
- To provide resources, personnel, and budget to the extent necessary to fulfill the tasks and achieve them